- MONTH
- YEAR
An Illusion of Managed Interdependence. A Transatlantic Tech Partnership
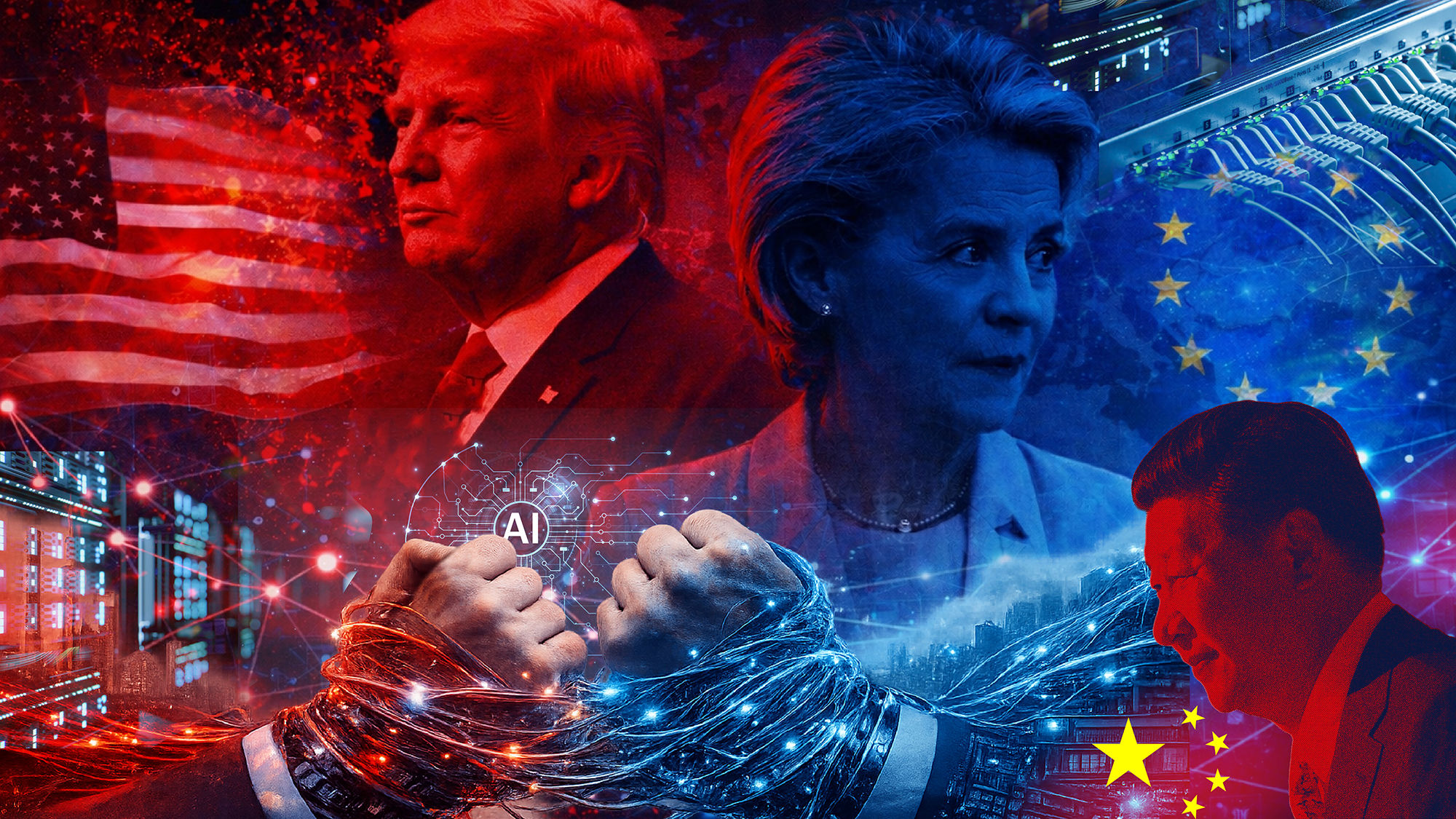
A report by German Marshall Fund analysts, entitled A Transatlantic Tech Partnership, analyzes the IT technology standoff between the USA and China and Europe’s groping for a place in this race. The authors emphasize that the USA is striving for ‘unquestioned and unchallenged global dominance’ in the AI field, while China aims to achieve AI leadership by 2030. Against this backdrop, Europe depends on external, mainly U.S., suppliers for 80 percent of its digital stack. The report aims to justify the need for ‘managed interdependence’ with the U.S. IT industry instead of trying to achieve full autonomy.
The authors argue that full technological sovereignty would cost Europe EUR 4 trillion at a time when it is also attempting to rearm. Advocates of decoupling should realize that the burden would fall on the budget at precisely the moment when the continent is trying to step up military spending. The report stresses that integration is deep and cannot be broken up without catastrophic losses for both parties. Advanced US-designed chips are impossible without German lasers and Dutch ASML lithography. The 5G telecommunications equipment segment of the U.S. market is dominated by Ericsson and Nokia that are a good alternative to Chinese expansion into that segment. An attempt to recreate parallel technology stacks on both sides of the Atlantic would take resources away from what is really important: funding for breakthrough research. The scale required for leading firms to compete with China’s State-backed technology ecosystem would shrink.
The authors insist that the United States and China are not equivalent risks. All the reasoning is based on the difference between their political and legal systems.
China’s 2017 National Intelligence Law requires Chinese companies to cooperate with the intelligence service and share data with the State. And the USA is pluralistic in that private companies (such as Microsoft and Google) regularly contest the government’s demands in court and have financial incentives to defend global trust in their products. In this way, the authors argue that the USA offers independent challenging channels that are lacking in China, which makes the American dependence ‘safer’. Consequently, dependence on U.S. technology is felt structurally less dangerous to sovereignty than Chinese vendors’ penetration.
In the authors’ opinion, governments should take stock of their technology stacks and draw clear distinctions among what requires sovereign control, what can be safely sourced from trusted partners and what remains substitutable. Transparency would reduce geopolitical friction. As examples of mechanisms that are already operational they cite hybrid cloud projects; a partnership between SAP, Deutsche Telekom and NVIDIA; a joint initiative between Delos Cloud GmbH and Microsoft; and the work of the German BSI (Federal Office for Information Security) with Amazon Web Services to explore encryption and standards for sensitive public-sector use. Those models enable Europe to quickly adopt AI tools without losing all control of infrastructure.
The facts cited in the document suggest a number of conclusions that stretch beyond its stated agenda.
European élites are methodically being led to think that working for complete IT sovereignty is an economic madness. The amount of EUR 4 trillion is not an assessment but a nearly prohibitive warning. The mutual dependence argument is convenient but asymmetrical. Control over the software architecture, cloud protocols and API standards belongs to Washington. It is the leverage, while Europe’s specialization in hardware is a supplier function. Historical experiences of sanction pressure (ASML and exports to China) demonstrate who precisely defines the limits of what is permitted.
‘Managed interdependence’ is worded this way to semantically camouflage inevitable technological subordination. Hybrid clouds with Microsoft or AWS mean data and processes placed on external infrastructure where control over the hypervisor, security patches and updates remains with the vendor from another jurisdiction. And Microsoft’s or Google’s corporate pluralism, so much trusted by the authors, ends where Pentagon contracts become a priority and the National Security Council issues its directives.
The authors suggest giving control over key nodes of the ‘digital house’ to an external ‘security firm’, ostensibly to protect it from ‘robbers in the next street’. The question of who will secure you against the security guard is removed from the agenda.
Yet the document itself admits that technology leverage is a weapon – and cites incidents with the International Criminal Court and Greenland. However, Europe’s proposed response falls short of creating protective mechanisms. What is suggested is to integrate into the system so that the lever is spearheaded exclusively against Beijing. In such an architecture, Europe’s role is reduced to being a market springboard and a sanction coercion tool.